Why Your Network Security Key Is More Than Just a Password: Understanding Its Importance

Network security keys allow users to establish a secure connection to protect them from cyberattacks while online. The terms “network security key” and “password” are often used interchangeably, but this can be misleading. There are different types of security keys, with new technology just recently released.
What is a Network Security Key
A network security key is a password you use to connect to a wireless network. It helps protect your Wi-Fi by preventing unauthorized people from accessing your internet and data.
Secure network connections are vital with the growing use of hotspots, home networks, and the contemporary near-total reliance on online resources. The right network security key can help achieve safe, secure networks. Keep reading to learn the basics about network security keys and to understand the similarities and differences with passwords.
Purpose of a Network Security Key
Just like you need a key to enter the locked, front door of your house, you need a security key to gain access to a network. The network security key is a network password or passphrase used to provide authorization for a user to use a device on a local area network (LAN).
For the owner of the network, the network key prevents unauthorized access. For users, the key gives them confidence their information is safe and protected while using the internet.
Where and How are Network Security Keys Used?
The most familiar application of network keys today is with private networks, such as a home network. A printer, smart TV, smartphone, and other devices all connect to the router forming the personal network. The router is in turn connected to the modem which brings internet service into the house.
Network Security Keys at Home
In order to gain access to the internet, you first need to connect your device to Wi-Fi. To use your iPhone or iPad, for example, you will go to settings to enter the network security key (or wireless password). The key you enter allows your Wi-Fi router to “talk” to the devices, thus, allowing you to get online. Your sister, mother, and anyone else who wants to join your home Wi-Fi will enter the same network security key across their connected devices as well.
Network Security Keys at Work
Small business networks follow the same structure as home networks. However, with most businesses now offering customers free Wi-Fi access, or hotspots, they typically establish a two-router network. The public would then access the Wi-Fi network via one router, whereas the business operations would be kept private using a different network security key on the other router.
Customers could access the Wi-Fi from their Chromebook, PC, Mac, or mobile device by selecting the name of the public Wi-Fi hotspot (SSID) from the list displayed in the wireless settings, enter the Wi-Fi password (network security key), and connect. Your business’s private network would be visible, but not accessible since your network security key would not be known to your customers.
So Isn’t a Network Security Key Just a Password?
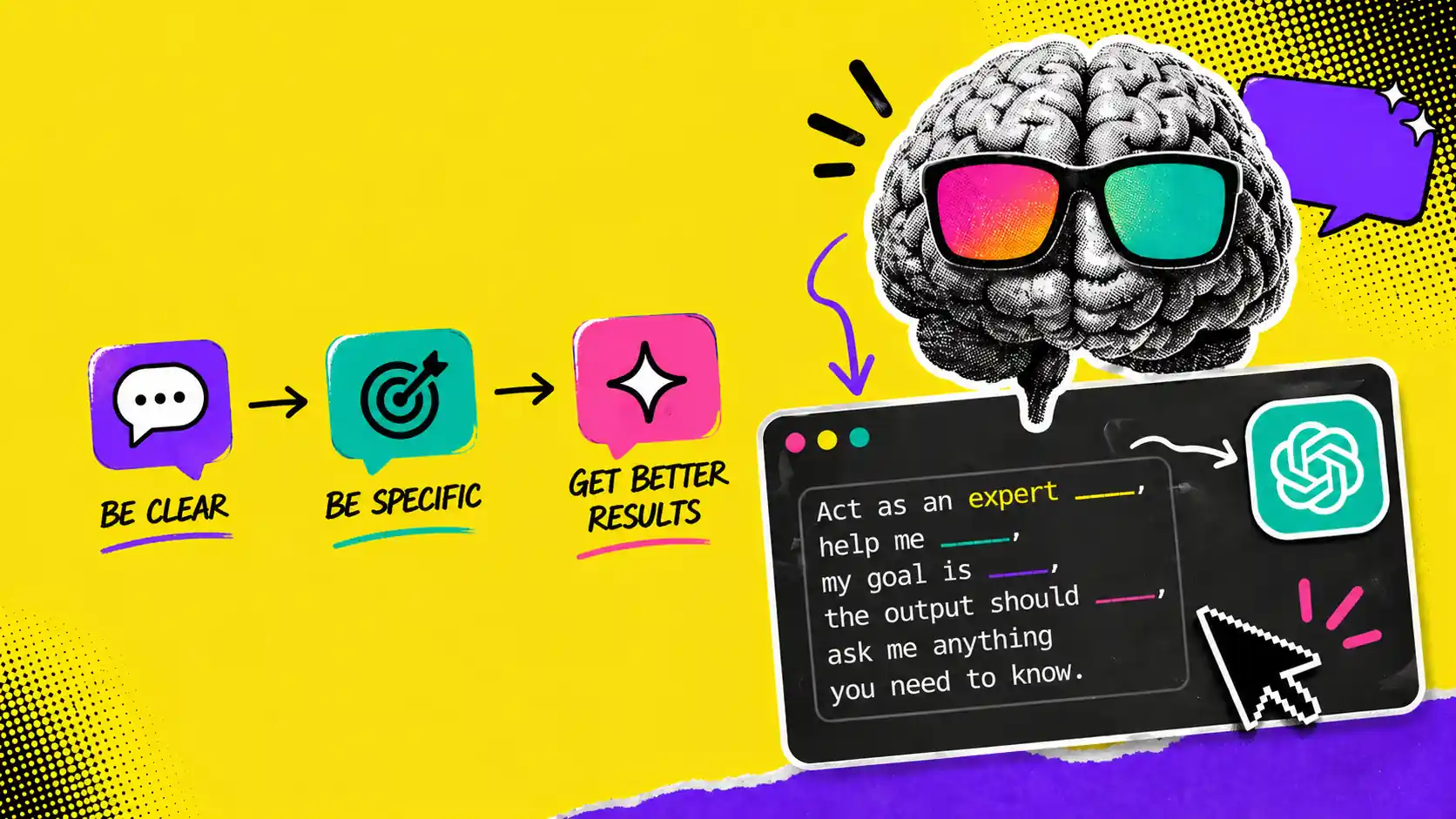
Not exactly. A security key may sound a lot like a password, in fact, we even use ‘password’ in the definition, and it is entered like a password, but a security key is so much more. The security key is a technical term associated with hardware, like wireless routers and modems. Each network, then, has a different type of security key depending on the maker of the network device.
A network security key is the encryption key that protects your internet. Security keys can be viewed as cybersecurity tools that are critical for protecting against nefarious entities that might seem to collect personal information, steal identities, compromise financial data, and silently listen to—or watch—users. In other words, according to the U. S. Department of Homeland Security, using the appropriate network security key prevents unauthorized users from accessing and viewing your data.
The network administrator has full control of network security keys and network settings, and can control whether a user can get onto the internet. Network administrators should select the highest level of security available to protect their business data and the users. The type of security key and a strong password determine how safe the network is from hackers.
Different Types of Network Security Keys
The most common types of network security keys that provide authorization to wireless networks and help protect confidential data are Wi-Fi Protected Access (WPA), Wi-Fi Protected Access 2 (WPA2), and Wired Equivalent Privacy (WEP).
Security Level: Generally considered insecure due to vulnerabilities and is not recommended for modern networks.
WEP (Wired Equivalent Privacy):
WEP keys are the earliest form of network security keys, and are now being phased out. The WEP encryption method allows everyone using the key to see other user’s information and security flaws in it made for an easy target for hackers.
Security Level: Offers better security than WEP but is still less secure than WPA2.
WPA and WPA2 (Wi-Fi Protected Access & Wi-Fi Protected Access II)
WPA and WPA2 keys are upgrades to WEP requiring a network security key in order to initiate access to the network. For both of these keys, after the validation, the exchange of data between the host device and the access point is encrypted.
WPA2 is a more secure upgrade to WPA using an advanced encryption standard (AES)-based encryption mode. WPA and WPA2 are used for home networks and small-scale office networks.
Security Level: Highly secure with strong encryption, making it the preferred choice for most networks.
WPA3 (Wi-Fi Protected Access III)
WPA3 is the most recent, and offers the strongest encryption, but is not widely available.
You can check which security method is enabled and find your network security key by accessing your router and looking at the manufacturer’s sticker. See this article on Lifewire for information on finding keys on your router, Windows 10, and Android devices.
Security Level: Offers the highest level of security currently available for wireless networks.
How Network Security Keys Work:
- Encryption: The key encrypts data transmitted between a device and the wireless router, ensuring that even if data is intercepted, it cannot be easily read by unauthorized parties.
- Authentication: Devices must provide the correct network security key to connect to the network, which helps prevent unauthorized access.
Importance of Network Security Keys:
- Protects Data: Encrypts your data to prevent eavesdropping and data theft.
- Prevents Unauthorized Access: Ensures only authorized users can access your network, preventing bandwidth theft and potential security breaches.
- Enhances Privacy: Keeps your internet activities private from unauthorized users who might try to spy on your network traffic.
Keep Your Networks Safe and Secure
Your network security keys may be determined by your company’s security protocol or may even be mandated by government regulations. Whatever option you have, ensure all known vulnerabilities are addressed.
Compare different hosting, network, and VPN services, explore our in-depth reviews & informative articles, and choose the best solution for you. Sonary provides you the knowledge you need to make informed and faster decisions.
We offer software reviews for different point-of-sale (POS) software solutions, sales, marketing, and more.