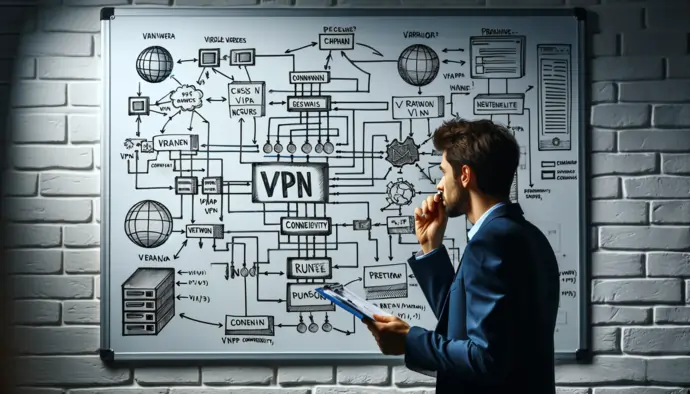
How To Use a VPN Safely and Effectively in 2026

According to researchers at security.org, 85% of adult internet users are mindful of VPNs. In 2020, 49% of users used a VPN for general purposes, and 3% utilized it to keep their journalism, whistleblowing, and activism work confidential. As per the Pre-Pandemic State of VPN Report published by Security Magazine, the Top three use cases of VPN are remote access (83%), site-to-site connections (57%), and site-to-cloud or/and cloud-to-cloud connections (48%).
VPN utilizes the IP Security Architecture (IPSec) open framework and runs on the network layer of the TCP/IP communication stack model. Moreover, it supports Layer 2 Tunnel Protocol (L2TP), a virtual line. The L2TP offers cost-effective remote access by enabling a corporate network server to manage IP addresses that have been assigned to its remote workforce.
The article will explore the content about VPN basics, what it is, how does VPN work, how can I use the VPN, how to set up a VPN at home, VPN remote access, VPN tunneling, how to connect to a VPN, remote access VPN, VPN benefits, and more.
What Is a VPN and How Does It Work?
What Is a VPN?
The Virtual Private Network (VPN) provides you with secure point-to-point communication over the public internet. VPNs have gained tremendous popularity and are used primarily for e-commerce and telecommuting. VPN has become a vital component in a corporate perimeter security configuration. VPNs protect network traffic with essential activities, including encrypted authentication, data payload encryption, and IP encapsulation.
How Does It Work?
Every individual or company with private data in transit wants to know whether VPNs really work? So, the answer is YES. Usually, the Internet Service Provider (ISP) assigns an IP address through a server when a computer connects to the internet. However, this is not the case when a user utilizes a VPN. Instead, the VPN assigns an IP address via a VPN’s private server, which may be located in different counties rather than a user’s home country. In this way, a user will remain anonymous, and no one can identify his exact location and intercept his data traffic. In simple words, the VPN routes a user’s internet connection through his chosen private server rather than the one selected by the ISP.
What is a VPN tunnel? VPNs create a VPN tunnel, a secure encrypted path to transmit data over the internet. This process is known as VPN tunneling. VPN encryption hides or encrypts data using a public or private key (decryption keys), which is only known by the user’s computer or a VPN server. When the encrypted data arrives at the destination, a user will use the decryption keys to unlock this data or decrypt data from cyphertext to plaintext. A VPN often hides your browsing history, devices, location for sharing, IP address and location, and web activity.
Best VPNs Software
 Connect to over 94 countries
Connect to over 94 countries  High speed streaming: Netflix, Disney+, HBO
High speed streaming: Netflix, Disney+, HBO  Ultra-fast speeds
Ultra-fast speeds  3200+ servers in 65 countries
3200+ servers in 65 countries  Connect up to 6 devices simultaneously
Connect up to 6 devices simultaneously  Browse the internet with total privacy
Browse the internet with total privacy How To Use a VPN?
Typically, using a VPN doesn’t require a tech-savvy or lengthy tutorial. Instead, you need to follow simple steps to set up and use your VPN. The subsequent sections will take a deep dive into this regard.
1. Getting VPN
First and foremost, you need to choose the right VPN that best caters to your business needs. For example, you need to consider whether your chosen VPN is hardware-based, such as just configured on a router, software-based, or both. Plus, you need to make sure that your chosen VPN works with any computers or different operating systems. Finally, VPN must provide enough speed and powerful features. We recommend choosing from some top-notch VPNs, such as NordVPN and ExpressVPN.
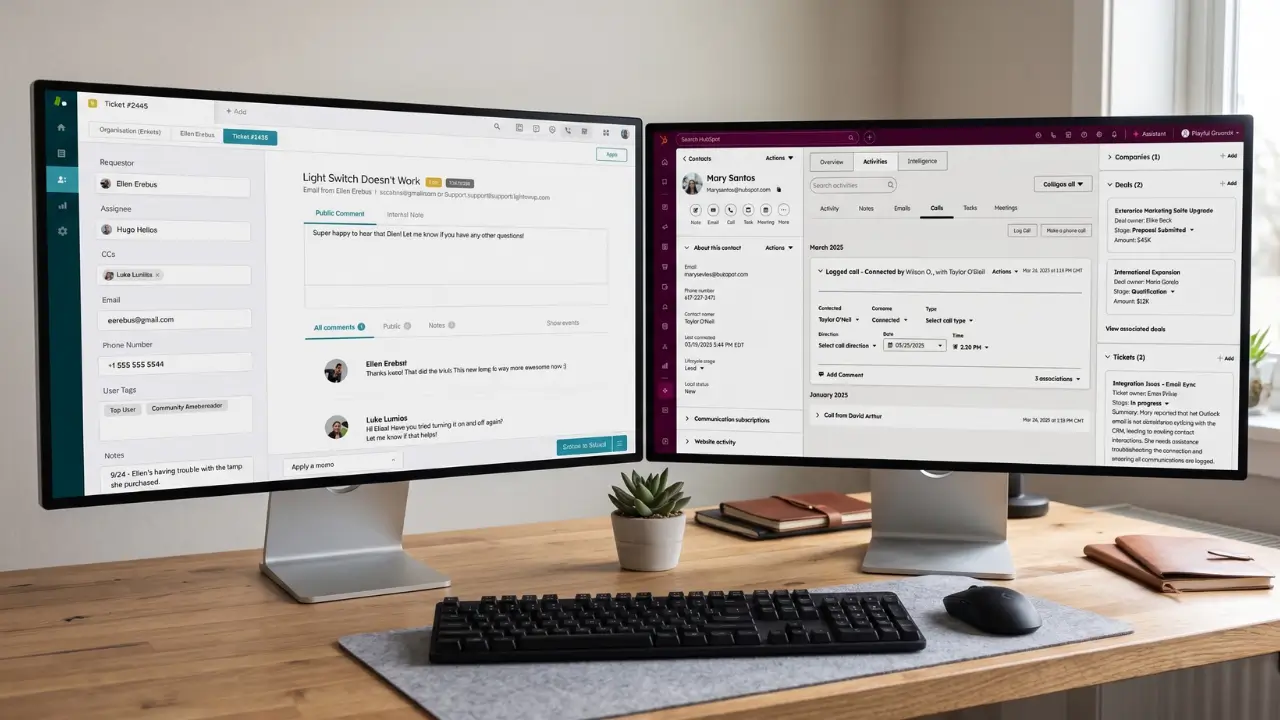
2. Setting up VPN
Setting up a VPN is no longer a difficult task. First, download the VPN app from their official website, follow the installation process, and sign in to the app with your account.
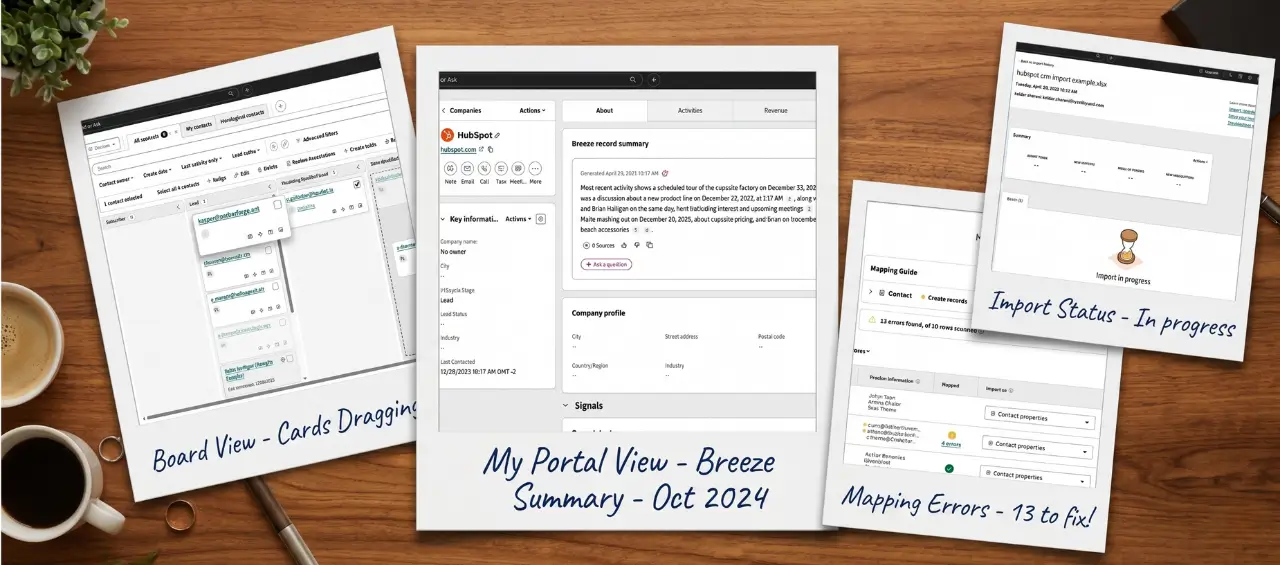
3. Choosing a Server
Your VPN provider offers multiple regions for VPN connection. You can browse the list of countries or regions provided by your VPN app. In addition, you can choose your desired location from the app.
Why Use a VPN at Home?
Using a VPN at home is unnecessary as you protect your home network with a password. Therefore, there is no need for an extra layer of security through a VPN. However, you can use the VPN to unlock the content related to sports or streaming. In addition, a remote VPN provides secure access for employees working remotely by encrypting all the traffic the user sends and receives.
How To Connect to Office Network from Home Using VPN?
A VPN can provide you with a secure connection to your office network from home. To this end, you need to follow some steps, such as:
- Get a VPN-enabled router
- Set up a VPN using a quick-start wizard
- Select security settings
- Enable users
- Connect
How Can I Use VPN NAT?
VPN NAT has two different types: VPN NAT prevents IP address conflicts, and VPN NAT hides local addresses. The following sections delve into more detail.
Using VPN NAT to Prevent Conflicts Between IP Addresses
NAT stands for Network Address Translation. IP address conflicts often occur when a user configures the VPN connection between systems or networks with a similar addressing scheme. For example, both organizations need to create VPN connections by employing one of the designated ranges of a private IP address. Under such circumstances, VPN NAT can help you prevent IP address conflicts.
Using VPN NAT to Hide Local Addresses
VPN NAT can hide the actual IP address of a user’s local system. For this to be done effectively, the VPN NAT will translate the IP address of a local system to another IP address that you have made available publicly. When a user configures the VPN NAT, he can particularize that each publicly known IP address is translated to one of the pools of the hidden IP addresses.
Related Articles
Why Is It Necessary to Use a VPN?
Using a VPN is indispensable to avoid data breaches and other security incidents. Look at the following sections to explore VPN benefits.
Online Security
Public WiFi or hotspot is always vulnerable. For example, if you use public WiFi at a restaurant or airport, you must know that this connection is not encrypted. Don’t put your sensitive data on the verge of destruction. However, a reliable VPN product, such as VPN Proxy Master, can protect your network traffic through robust encryption and ensure the overall security of your computer, tablet, or mobile device.
Exploring Dark Web
People commonly say that browsing the dark web is a serious crime involving illegal content, such as child pornography, drug trafficking, and arms sale. Contrarily, researchers may use the dark web for research purposes, which is positive. But you cannot take the risk of using it without a VPN that can provide you with a secure connection over the internet.
Accessing Blocked Content
Some content may not be accessible in specific regions or countries. For example, you cannot watch some Netflix movies in certain countries. However, a VPN can resolve this issue by unblocking this geo-blocked content.
Unblocking All Websites
VPN unblocks all websites. For example, your company may not allow you to access social media during office hours. However, VPN can unblock all social media sites.
The Bottom Line
You may want to access web pages or content on the internet, but security is the main issue. You also want to remain anonymous and don’t want to share your sensitive information with others. You may also want to unblock all the sites available on the internet. However, it’s not possible with traditional computer security. Instead, it would be best to have a strong VPN connection rich in features and provides enough speed and compatibility.